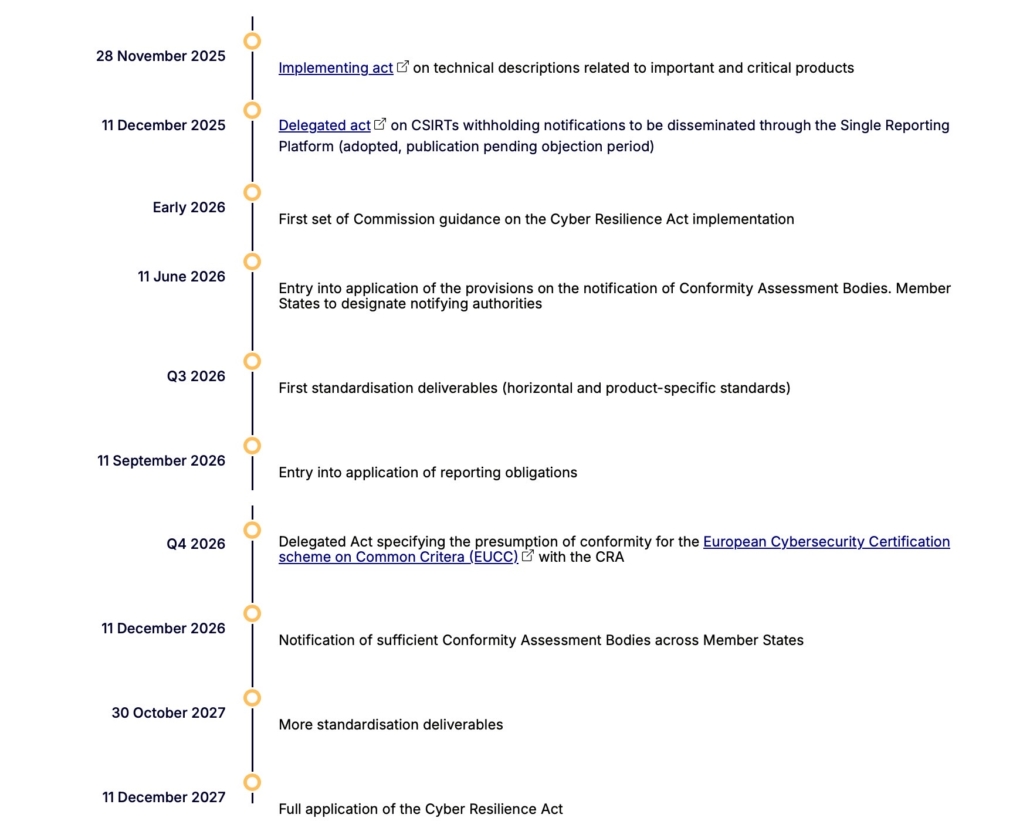
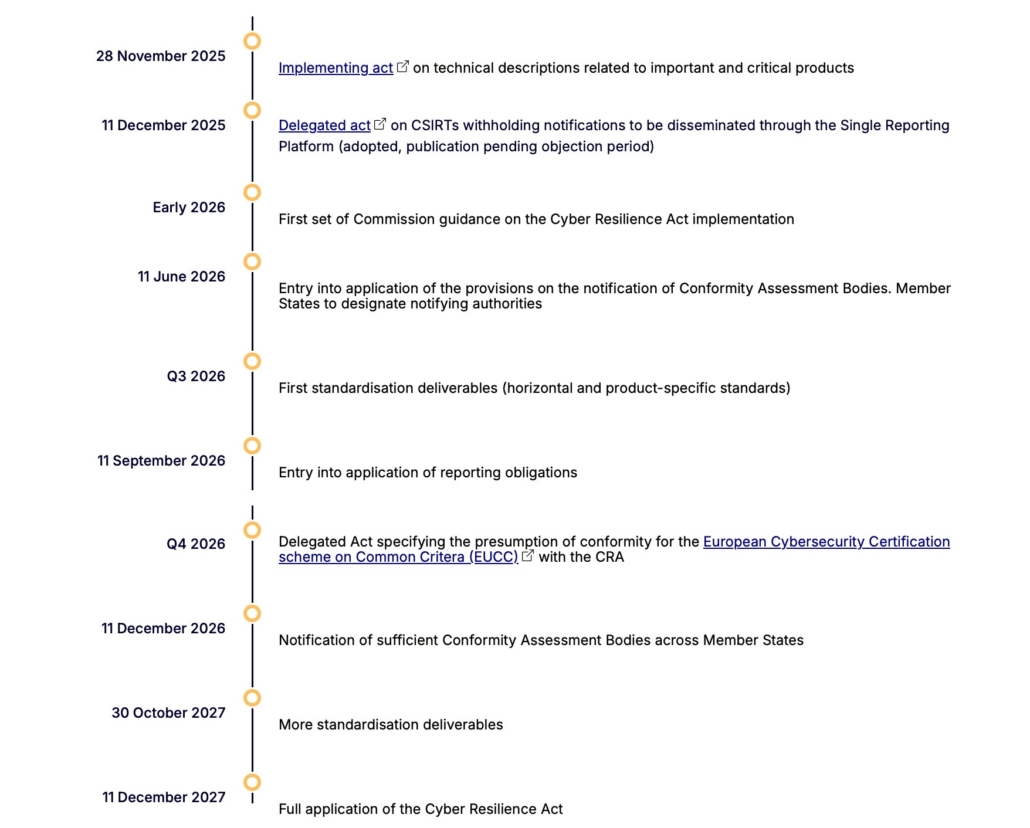
【EU CRA】 Reporting Guide: Mandatory 24-Hour Notification Starts September 11, 2026
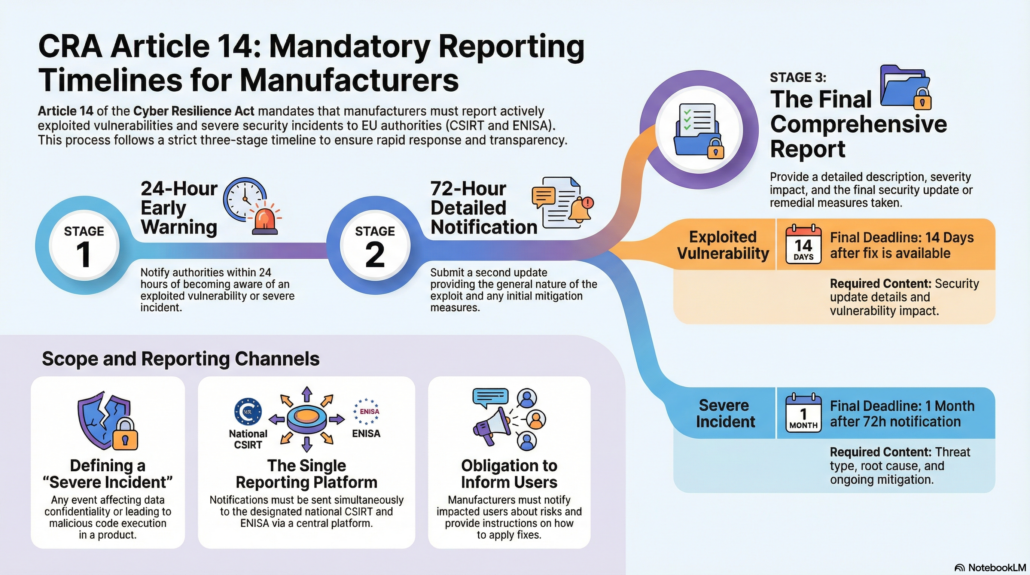
As the European Union moves toward the full implementation of the Cyber Resilience Act (CRA), the European Commission has clarified the mandatory reporting obligations for products with digital elements. Starting September 11, 2026, manufacturers must comply with rigorous timelines for reporting actively exploited vulnerabilities and severe security incidents.
1. The “24-Hour” Compliance Challenge
Under the CRA, the window for reporting is exceptionally narrow. Manufacturers must implement a multi-stage notification process:
- Early Warning (24 Hours): Within 24 hours of becoming aware of an actively exploited vulnerability or a severe incident, an initial alert must be submitted.
- Full Notification (72 Hours): A detailed analysis of the incident/vulnerability must follow the early warning.
- Final Report: For vulnerabilities, a report is due 14 days after a corrective measure (patch) is available; for severe incidents, the deadline is one month.
2. Centralized Compliance via the Single Reporting Platform (SRP)
To streamline the process, ENISA is developing the CRA Single Reporting Platform (SRP).
- One-Stop Reporting: Manufacturers will report only once through the SRP. The notification is automatically routed to the relevant Computer Security Incident Response Team (CSIRT) and ENISA simultaneously.
- Operational Timeline: The platform will be fully operational by September 11, 2026. A testing phase will precede the launch, allowing manufacturers to dry-run their reporting pipelines.
3. Critical Implications for Product Certification
From a certification perspective, “Compliance” now extends beyond the physical product to the manufacturer’s operational lifecycle:
- Vulnerability Management Audits: During the conformity assessment process, manufacturers must demonstrate they have the internal infrastructure to detect and report incidents within the 24-hour threshold.
- SBOM and Supply Chain Transparency: Rapid reporting is impossible without a comprehensive Software Bill of Materials (SBOM). Certification will increasingly depend on a manufacturer’s ability to map their software supply chain accurately.
- Cross-Border Information Sharing: While information is generally shared across EU member states immediately, a delegated act adopted in December 2025 allows CSIRTs to delay dissemination under specific cybersecurity grounds to prevent further exploitation.
如有任何問題,歡迎聯繫我們
電郵:Charles.liao@theonelab.co
電話:(02)8601-2828